Creating a root authority
A root Certificate Authority (CA) is the topmost entity in a hierarchy of digital certificates that establishes trust in a Public Key Infrastructure (PKI). The root CA issues and signs certificates for intermediate or issuing subordinate CAs, which in turn can issue certificates to end-users, servers, or devices.
To create a root CA:
-
Follow the steps described in Accessing your partitions to log into the PKIaaS interface as a user with any of these roles:
-
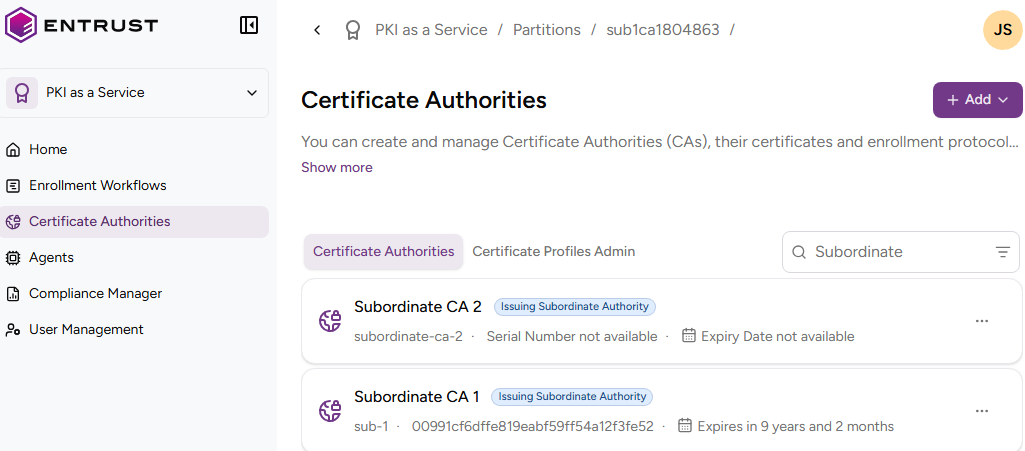
Click Certificate Authorities in the sidebar.
-
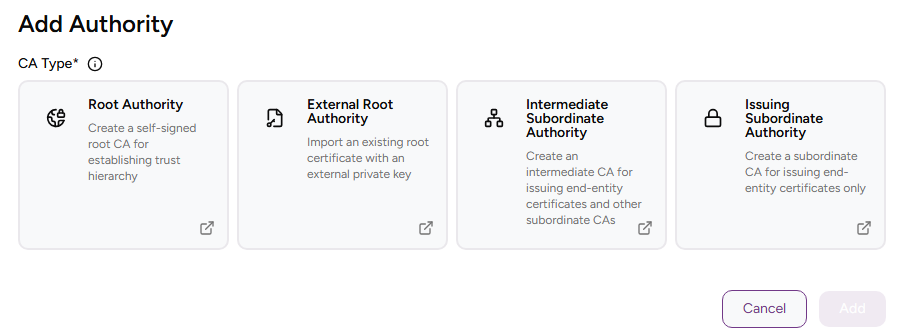
Click Add and select Certificate Authority.
-
Select Root Authority.
-
Click Add and complete the following values.
-
Click Create.
-
Check the details of the created CA — for example, the Serial Number of the Certificate Signing Certificate.
CA Identifier
Write a unique identifier for the new CA in your PKI hierarchy. This identifier:
- Must contain 2-18 characters
- Can only include lowercase letters, numbers, hyphens (’-’), and underscores (’_')
ℹ After deleting a CA, wait 24 hours before creating a CA with the same identifier.
Friendly Name
Write a descriptive name for the CA in your PKIaaS partition.
Signing Key Details
Select a combination of cryptosystem and hash algorithm for the new CA to sign certificates.
ℹ The production release does not yet support some of the combinations listed below.
| Label | Key algorithm | Signature algorithm | VA key type | VA signature algorithm |
|---|---|---|---|---|
| RSA-2048+PKCS15-SHA256 | RSA2048 | sha256WithRSAEncryption | RSA2048 | sha256WithRSAEncryption |
| RSA-2048+PSS-SHA256 | RSA2048 | sha256WithRSAPSS | RSA2048 | sha256WithRSAPSS |
| RSA-3072+PKCS15-SHA256 | RSA3072 | sha256WithRSAEncryption | RSA2048 | sha256WithRSAEncryption |
| RSA-3072+PSS-SHA256 | RSA3072 | sha256WithRSAPSS | RSA2048 | sha256WithRSAPSS |
| RSA-4096+PKCS15-SHA512 | RSA4096 | sha512WithRSAEncryption | RSA2048 | sha256WithRSAEncryption |
| RSA-4096+PSS-SHA512 | RSA4096 | sha512WithRSAPSS | RSA2048 | sha256WithRSAPSS |
| ECDSAP256+SHA256 | ECDSAP256 | ecdsa-with-SHA256 | RSA2048 | sha256WithRSAEncryption |
| ECDSAP384+SHA384 | ECDSAP384 | ecdsa-with-SHA384 | RSA2048 | sha256WithRSAEncryption |
| ECDSAP521+SHA512 | ECDSAP521 | ecdsa-with-SHA512 | RSA2048 | sha256WithRSAEncryption |
| ML-DSA-44 | ML-DSA-44 | ML-DSA-44 | RSA2048 | sha256WithRSAEncryption |
| ML-DSA-65 | ML-DSA-65 | ML-DSA-65 | RSA2048 | sha256WithRSAEncryption |
| ML-DSA-87 | ML-DSA-87 | ML-DSA-87 | RSA2048 | sha256WithRSAEncryption |
| Hash-SLH-DSA-SHA2-128s-With-SHA256 | Hash-SLH-DSA-SHA2-128s-With-SHA256 | Hash-SLH-DSA-SHA2-128s-With-SHA256 | RSA2048 | sha256WithRSAEncryption |
| Hash-SLH-DSA-SHA2-128f-With-SHA256 | Hash-SLH-DSA-SHA2-128f-With-SHA256 | Hash-SLH-DSA-SHA2-128f-With-SHA256 | RSA2048 | sha256WithRSAEncryption |
| Hash-SLH-DSA-SHA2-192s-With-SHA512 | Hash-SLH-DSA-SHA2-192s-With-SHA512 | Hash-SLH-DSA-SHA2-192s-With-SHA512 | RSA2048 | sha256WithRSAEncryption |
| Hash-SLH-DSA-SHA2-192f-With-SHA512 | Hash-SLH-DSA-SHA2-192f-With-SHA512 | Hash-SLH-DSA-SHA2-192f-With-SHA512 | RSA2048 | sha256WithRSAEncryption |
| Hash-SLH-DSA-SHA2-256s-With-SHA512 | Hash-SLH-DSA-SHA2-256s-With-SHA512 | Hash-SLH-DSA-SHA2-256s-With-SHA512 | RSA2048 | sha256WithRSAEncryption |
| Hash-SLH-DSA-SHA2-256f-With-SHA512 | Hash-SLH-DSA-SHA2-256f-With-SHA512 | Hash-SLH-DSA-SHA2-256f-With-SHA512 | RSA2048 | sha256WithRSAEncryption |
| Hash-SLH-DSA-SHAKE-128s-With-SHAKE128 | Hash-SLH-DSA-SHAKE-128s-With-SHAKE128 | Hash-SLH-DSA-SHAKE-128s-With-SHAKE128 | RSA2048 | sha256WithRSAEncryption |
| Hash-SLH-DSA-SHAKE-128f-With-SHAKE128 | Hash-SLH-DSA-SHAKE-128f-With-SHAKE128 | Hash-SLH-DSA-SHAKE-128f-With-SHAKE128 | RSA2048 | sha256WithRSAEncryption |
| Hash-SLH-DSA-SHAKE-192s-With-SHAKE256 | Hash-SLH-DSA-SHAKE-192s-With-SHAKE256 | Hash-SLH-DSA-SHAKE-192s-With-SHAKE256 | RSA2048 | sha256WithRSAEncryption |
| Hash-SLH-DSA-SHAKE-192f-With-SHAKE256 | Hash-SLH-DSA-SHAKE-192f-With-SHAKE256 | Hash-SLH-DSA-SHAKE-192f-With-SHAKE256 | RSA2048 | sha256WithRSAEncryption |
| Hash-SLH-DSA-SHAKE-256s-With-SHAKE256 | Hash-SLH-DSA-SHAKE-256s-With-SHAKE256 | Hash-SLH-DSA-SHAKE-256s-With-SHAKE256 | RSA2048 | sha256WithRSAEncryption |
| Hash-SLH-DSA-SHAKE-256f-With-SHAKE256 | Hash-SLH-DSA-SHAKE-256f-With-SHAKE256 | Hash-SLH-DSA-SHAKE-256f-With-SHAKE256 | RSA2048 | sha256WithRSAEncryption |
| SPHINCS+-SHA2-128f-simple | SPHINCS+-SHA2-128f-simple | SPHINCS+-SHA2-128f-simple | RSA2048 | sha256WithRSAEncryption |
| SPHINCS+-SHA2-128s-simple | SPHINCS+-SHA2-128s-simple | SPHINCS+-SHA2-128s-simple | RSA2048 | sha256WithRSAEncryption |
| SPHINCS+-SHA2-192f-simple | SPHINCS+-SHA2-192f-simple | SPHINCS+-SHA2-192f-simple | RSA2048 | sha256WithRSAEncryption |
| SPHINCS+-SHA2-192s-simple | SPHINCS+-SHA2-192s-simple | SPHINCS+-SHA2-192s-simple | RSA2048 | sha256WithRSAEncryption |
| SPHINCS+-SHA2-256f-simple | SPHINCS+-SHA2-256f-simple | SPHINCS+-SHA2-256f-simple | RSA2048 | sha256WithRSAEncryption |
| SPHINCS+-SHA2-256s-simple | SPHINCS+-SHA2-256s-simple | SPHINCS+-SHA2-256s-simple | RSA2048 | sha256WithRSAEncryption |
| Falcon-512 | Falcon-512 | Falcon-512 | RSA2048 | sha256WithRSAEncryption |
| Falcon-1024 | Falcon-1024 | Falcon-1024 | RSA2048 | sha256WithRSAEncryption |
| MLDSA44-RSA2048-PKCS15 | MLDSA44-RSA2048-PKCS15 | MLDSA44-RSA2048-PKCS15 | RSA2048 | sha256WithRSAEncryption |
| MLDSA44-RSA2048-PSS | MLDSA44-RSA2048-PSS | MLDSA44-RSA2048-PSS | RSA2048 | sha256WithRSAPSS |
| MLDSA44-ECDSA-P256 | MLDSA44-ECDSA-P256 | MLDSA44-ECDSA-P256 | RSA2048 | sha256WithRSAEncryption |
| MLDSA65-RSA3072-PKCS15 | MLDSA65-RSA3072-PKCS15 | MLDSA65-RSA3072-PKCS15 | RSA2048 | sha256WithRSAEncryption |
| MLDSA65-RSA3072-PSS | MLDSA65-RSA3072-PSS | MLDSA65-RSA3072-PSS | RSA2048 | sha256WithRSAPSS |
| MLDSA65-RSA4096-PKCS15 | MLDSA65-RSA4096-PKCS15 | MLDSA65-RSA4096-PKCS15 | RSA2048 | sha256WithRSAEncryption |
| MLDSA65-RSA4096-PSS | MLDSA65-RSA4096-PSS | MLDSA65-RSA4096-PSS | RSA2048 | sha256WithRSAPSS |
| MLDSA65-ECDSA-P384 | MLDSA65-ECDSA-P384 | MLDSA65-ECDSA-P384 | RSA2048 | sha256WithRSAEncryption |
| MLDSA87-ECDSA-P384 | MLDSA87-ECDSA-P384 | MLDSA87-ECDSA-P384 | RSA2048 | sha256WithRSAEncryption |
Expiry Date
Select an expiry date for the Certificate Signing Certificate of the new CA.
⚠ After the expiry date, the CA cannot operate if you have not renewed the CA certificate.
Enable CRL
This read-only box is always checked as PKIaaS authorities always provide a CRL publishing endpoint.
Enable OCSP
Check this box to enable an OCSP (Online Certificate Status Protocol) service for the new certificate authority.
ℹ This feature requires a subscription that includes the OCSP Service. See Checking your subscriptions for how to check your current subscription.
Certificate Profiles
Select the Authority certificate profiles the new root CA will support for issuing certificates to authorities.
- Click + to expand the profiles on the selected groups.
- Select the check boxes of the profiles you want to enable.
Subject
Enter a value for each RFC5280 attribute in the certificate subject’s Distinguished Name (DN).
| Field | Mandatory |
|---|---|
| Common Name | ✔ |
| Organization | ❌ |
| Organizational Unit | ❌ |
| State/Province | ❌ |
| Locality Name | ❌ |
| Domain Component | ❌ |
| Country | ❌ |
Alternatively, you can:
- Toggle the Advanced Subject switch
- Type a Distinguished Name (DN) including additional attributes.
The resulting Distinguished Name will uniquely identify the Certificate Signing Certificate of your new CA — for example:
CN=MyRootCA, O=MyOrganization, L=MyCity, ST=MyState, C=US